Imagery information is collected from many sources in many forms and stored in diverse formats and processed and stored at locations around the world. Archival imagery is routinely obtained from national intelligence sources in a variety of forms, mostly photographic prints, but increasingly it is found in digital electronic formats stored on tapes and disks. But much imagery information comes directly from the armed services, obtained from sensors on the ground, from aerial platforms or from orbiting satellites.
The sensors operate in different regions of the electromagnetic spectrum, including visible photographic, radar and infrared spectra. Imagery from each of these technologies has particular characteristics that sometimes act as checks against or augmentation for data derived from a specific imagery system. Area coverage, resolution and viewing geometry varies among collected images.
Fused ImageryFusing or correlating multispectral imagery offers numerous advantages. Through automated summing and averaging computational techniques, the quality of images in electronic digital formats is significantly improved. Through subtraction and ratio techniques, images can be compared to reveal changes or differences among images. Each of these analytical functions is increasingly being automated to enable more rapid and reliable imagery intelligence, surveillance and reconnaissance reporting.
Comparing it either to archival images or to those from other spectra to detect variations increases the value of imagery. The result is that only the variation may need to be communicated among network nodes.
Areas of particular interest within an image can be expanded for emphasis and enhancement. Entire images can be rotated, panned or scrolled (automatically) using a variety of readily available computer programs and techniques. By exploiting the advantages of multispectral imagery, artificial intelligence and correlation with archival images, analysts can greatly enhance the value of an individual or set of images collected.
Another variation in imagery collection is that some images are collected via electro-optic sensors, and others are captured on film. Images on film frequently are converted to electronic files at some point to capitalize on automated processing and exploitation tools. As digital camera technology advances, fewer film-based sensors will be used.
The time required to deliver collected images is a critical factor to its operational value. Ordinary facsimile services may suffice for some image dissemination requirements; but missions may require considerably more complex capabilities, such as the ability to manipulate and exploit the image file by operational planners or targeteers using automated work stations; or they may need to be viewable in high-resolution; or large-format hard copies may be needed for various purposes.
The capabilities of analysts, equipment and other tools in operational units also can vary. In some cases, the unit may have its own analysts and sophisticated exploitation capabilities to provide specialized products to satisfy unique requirements. Others may rely on specialists located elsewhere to point out important elements in an image. Consistency of imagery perspective is important for units that must fight together.
Imagery information support to defense users is a complex undertaking, involving a variety of levels of service to link sources and individual user units with many of these elements deployed all over the world. Therefore, adaptability must be a characteristic of the supporting information infrastructure.
The two principal constraints in providing requisite imagery support to national security units are the available technology and affordable infrastructure. Another particularly important constraint is the large amount of data present in images captured by modern sensors, as compared to capacities of available telecommunications circuits. Related to this telecommunications availability (sometimes called "bandwidth") issue are special security measures that must be imposed to protect knowledge of the capabilities of some sensors. This results in multiple security levels of imagery information.
Planners considering alternatives to improve performance of defense imagery information management functions must also take into account that many "legacy" imagery information processing and exchange suites are incompatible. Many systems were built around discrete solutions unique to a vendor. Some have inherent limitations, such as being based on dissimilar technology that sometimes limits efficient processing, enhancement or automated image exploitation.
As noted above, increasingly imagery is managed most easily in an electronic format as digital files. In electronic form, imagery can more efficiently be stored, retrieved, processed, enhanced and exchanged with geographically distributed sites using telecommunications circuits or networks. The proliferation and increasing capacities of microprocessors make these efficiencies possible. Automated "on-line" digital storage media such as imagery file servers, however, require significant investments and system integration.
The flow of imagery information is dynamic, complex and chaotic. It comes from all directions. Sources are located on the battlefield, in nearby aircraft, at locations thousands of miles away and at points in between. Therefore, users benefit from shared, distributed storage and retrieval facilities and applications connected in an internetwork enabling collaboration and sharing of automated services.
End users and sources have special system input/output capability requirements. These involve transferring sensor output into the system and intelligence products from the system to peripheral devices, such as printers, or through a transducer to some other media, such as a compact disk, tape cassette or paper hard copy. The necessity of transferring images to high-quality paper or transparency hard copies is particularly important for some users.
Potential Architectures
The Cohen-Clinger Act of 1996 requires the federal government to view modern information technology as an enabler of more efficient government services, as an enterprise. Increasingly the national security enterprise of the government, including the DoD, Military Departments and Intelligence Community, is striving to manage information (including imagery information) as an enterprise. Planning for government-wide imagery information management is proceeding at a rapid pace and with considerable success.
At least three service levels must be considered in planning for support to national security imagery information management requirements. One includes a special global high-capacity imagery dissemination service at special compartmented security levels.
This service must interconnect users at all echelons with others using standard dedicated telecommunications services and image processing components.
Another must exploit all available independent networks at distinct security levels with common interoperable telecommunications circuitry and processing equipment and software.
A third service involves exploitation of trusted multi-level secure (MLS) computing technology, as it is expected to emerge in coming decades. As trusted MLS processors and networks mature, an imagery management environment can be distributed across a worldwide-integrated MLS network infrastructure. This will enable the efficient sharing of imagery information from all sources, encapsulating them in a standard digital file format that can be stored on imagery file servers distributed among nodes of the integrated network.
A global, high-capacity special imagery exchange network is perhaps the most reliable and can support large volumes of imagery exchange services. However, it lacks flexibility, serves a restricted set of subscribers and would be expensive. In addition, because the national security enterprise already supports a variety of costly networks that cannot be interconnected, adding an additional independent network raises important interoperability and cost-effectiveness questions. The issue of burdening users with the administrative and logistical responsibilities for additional networks is also a factor.
Limitations in service flexibility and network adaptability can be serious, depending on the mission and functions of the operating unit, its telecommunications management resources, and the geographic area of a specific operation. Unnecessary duplication and associated costs become apparent when units operating side-by-side require completely separate supporting infrastructures and are incapable of interoperability.
In fact imagery information management can take place over common information infrastructure with other automated information systems using modern digital computers. This avoids the need for costly unnecessarily duplicative and inflexible special telecommunications infrastructures. Through a common integrated network, users can selectively obtain information according to current needs. Information also can be efficiently processed, exploited and exchanged.
By adopting a common operating environment operating across an integrated information infrastructure, providers and users of imagery information products and services can also share "computing power" distributed consistently across the enterprise. Such a paradigm also enables additional benefits of exploiting a variety of modern information management techniques to effectively reduce the actual amount of data that must be transported among imagery servers, processors and terminals. Users can select (or otherwise be provided) only essential elements of an image file or other reference data, which they then could compare to existing archival image files to discern more current information. Where entire files are necessary, they can apply increasingly efficient file and data communications compression techniques to reduce communications bandwidth requirements to transport the information.
Security constraints are manageable by applying existing and emerging information security tools and services. As MLS technology matures, imagery information file servers will be trusted to keep files of varying security levels separated, and trusted host-to-host computer communications security systems will separate information as it passes over local and wide area networks.
Pending the availability of fully capable MLS computers, the DoD has adopted a "defense-in-depth" information security management strategy which enables layers of security which can be modularly varied to provide multiple levels of security to support the needs of individual enclaves of subscribers as they exchange information across interconnected networks.
Alternative ApproachesThe Defense Information Systems Network, the DoD Information Infrastructure (DII) Common Operating Environment (COE), the DII Shared Data Environment (SHADE) and the DoD Information Assurance Program sponsored defense-in-depth security management strategy, together have begun to establish the enabling distributed integrated information infrastructure and services needed to expedite improvements in imagery information management across the national security enterprise. These are all consistent with and supported by the DoD Joint Technical Architecture.
Imagery information management planners are adopting and adapting the benefits offered by these joint services. They are also beginning to explore massively parallel computing and a variety of approaches to artificial intelligence for exploiting and enhancing visual information and collaborative approaches to sharing it across common information networks.
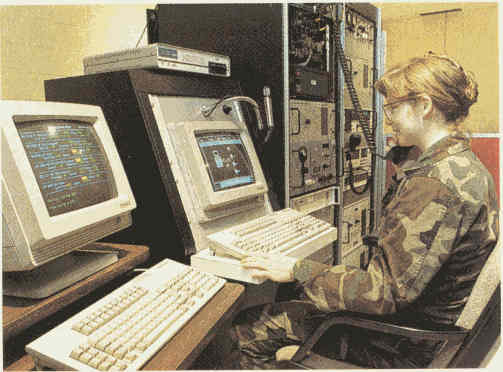
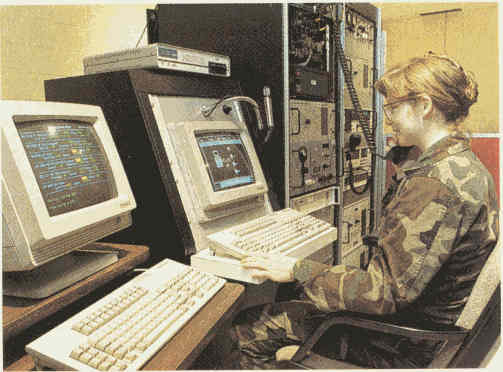
Multispectral imagery workstations offer dramatic improvement in the accuracy and utility of intelligence products. Image file servers, which can be connected to local and wide area networks, support these systems. The systems are beginning to be offered as commercial products that can operate independently, in tandem or as components of a distributed network.
The compact disc-read only memory, or CD-ROM, is another storage technology that has been exploited in recent years. This technology offers a valuable media for end-user storage of archival image files. With this system, updates from current imagery collection can be standardized to permit quick reference of changes. This further reduces the amount of data that must be transported among network nodes. Write once read many (WORM) drives are also used to store image files for future comparison, or for use in preparing intelligence products. All these automated tools are now widely available.
In addition to the emerging power of computers to perform sophisticated image processing and manipulation/enhancement, agreement on standard procedures, overlays, templates, icons, precisely measured graphic representations, structured reporting and similar techniques are being used to leverage computing power, while reducing the number of bits and bytes of data that must be exchanged among machines.
Non-Developmental SolutionsOf particular importance are end-user input and output capabilities required for entering images efficiently and accurately into the system and downloading them to appropriate media. Many users need large format and high-resolution printouts. These technologies are improving rapidly, and a variety of generic tools have been made available in recent years as affordable commercial products. Vendors are increasingly recognizing that management of standard interfaces and adherence to standard specifications for picture quality produce rapid results in affordably supporting customer requirements in a modular manner.
Imagery information system developers are providing near-term improvements to defense imagery information management by exploiting and building from existing approved programs using these commercial products and other non-developmental items. The defense agencies and armed services are adopting and adapting non-developmental solutions wherever possible to support defense programs already under way in a variety of disciplines. Individual projects are designed to improve the application of automated information processing to expedite and improve imagery exploitation. These include methods to improve object measurement, or mensuration, marginal enhancement, resolution enhancement, correlation and others, such as fusing imagery information with other information to produce "all-source" information products.
The challenge is to harness varied approaches to produce standard solutions that can be documented and applied to continue improvements to the common operating environment (COE). By exploiting the COE, information transport services of the DISN and other DoD-wide initiatives, component DoD organizations and other intelligence agencies of the federal government are able to expedite multiple programs capable of instituting an enterprise-wide national security imagery information management capability.
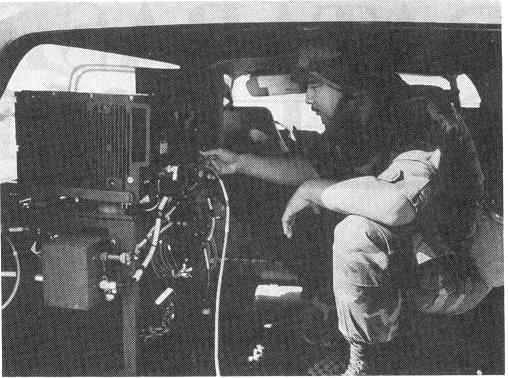
Imagery information systems are being consistently extended to tactical users and melded into their tactical information infrastructure. The military services have several programs underway to accomplish this, most oriented to integrated systems and networks that enable the efficient information management services anticipated by the Joint Staff's Joint Vision 2010 when information superiority is expected to enable dominance of friendly forces against future threats to our national security. In addition, a recent DoD initiative is leading to a DoD-wide information dissemination management program to ensure efficient management of DoD information infrastructure to provide improved awareness, availability and deliver of all types of information to operating forces and their supporting establishment.
